Third Party Integration Pentesting
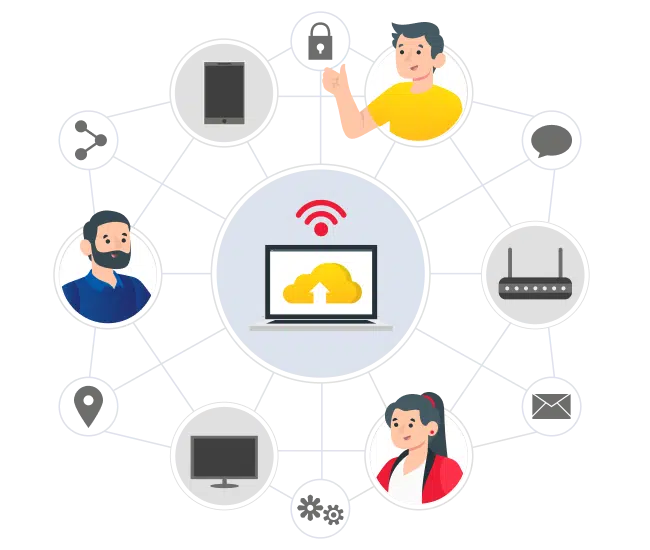
At Securityium, we understand the critical importance of securing third-party applications to protect organizations from cyber threats. Our methodology integrates the trusted OWASP standards with proprietary techniques specifically designed for third-party integrations. We utilize a robust toolkit comprising commercial, open-source, and custom-built tools to meticulously examine aspects such as authentication, authorization, cryptography, file management, and communication services. Our goal is to identify security risks associated with third-party integrations and ensure secure data exchange.
Third-Party Integration Penetration Testing (PT) evaluates the security of integrations between applications and third-party services or APIs. Our assessment identifies vulnerabilities like data exposure, authentication bypass, and insecure data transmission to ensure your integration practices are secure.